What is social engineering? It is a manipulative tactic used by cyber criminals to get unassuming victims to hand over confidential information whether it be login credentials, customer data, access to networks, or financial account numbers. At times, threat actors may try to convince their victims to give them access to their computer so that they may secretly install malware that can collect passwords and bank information.
Why do cyber thieves use social engineering? For starters, anyone can do it - no particular expertise or coding required. Second, it’s easy and effective. Ask any cyber security expert, and they will tell you that the weakest link on any front are humans who accept a social engineering attempt at face value. It doesn’t matter how many alarms you have installed or even armed security guards, if a victim trusts the message coming from the cyber criminal, they will let them in without hesitation or verification. As a result, every organization is vulnerable to social engineering.
You see, most people expect to look out for botnets or malware and ransomware, they’re not expecting an attack from a normal-looking message. Further, there is plenty of information online that cyber criminals can use to become even more convincing.
For instance, if they want to pretend they’re the CFO of a company, they can look up information on that CFO from social media, articles, job postings, dating sites, their relative’s social media profiles, and more. A little digging can provide a lot to a motivated social engineer. They gain victims’ trust through fear, helpfulness, respect for authority, and even greed. What would you do if you received a legitimate-looking email from a site saying you won a prize? How would you respond if a sincere-looking text message came from your boss saying they forgot a password and need your help?
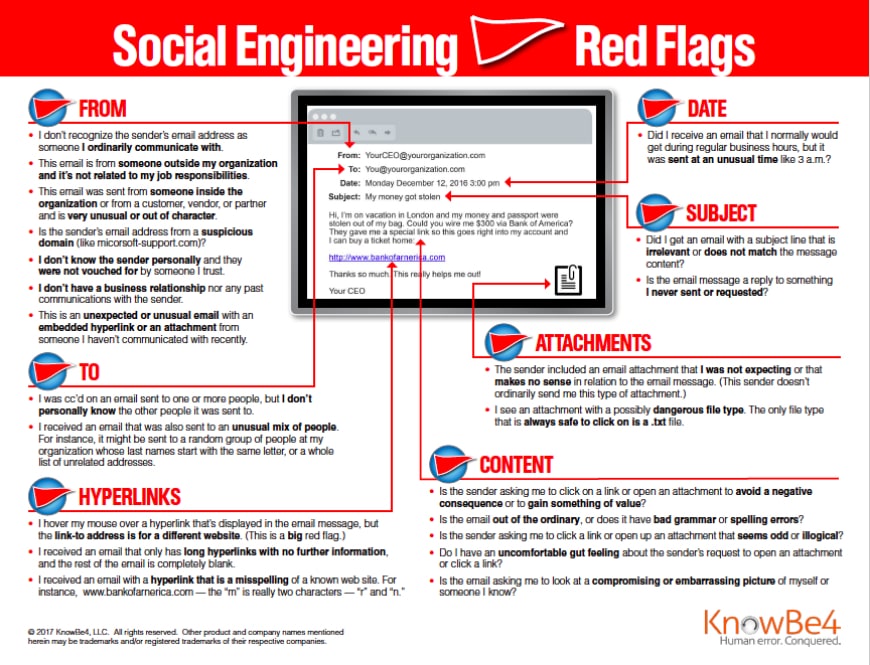
At some point, almost everyone will be targeted by a social engineering attack. Cyber security includes knowing who you can trust. So then, let’s dive into social engineering red flags.
- A message was sent after business hours, such as 3 a.m.
- You don't recognize the sender's address.
- The email is from someone outside of your work organization, and the question is not related to your work tasks.
- The email was sent from someone inside the organization, but the request was unusual.
- You don't not know the sender personally.
- The message was unexpected and included an embedded attachment or hyperlink.
- You were cc'd on an email from someone you don't know personally.
- The hyperlink leads to a different website than what is displayed in the email.
- The hyperlink is a misspelling of a popular website such as netflixx.com instead of netflix.com.
- The subject line does not match the text in the body.
- The message is a reply to something you never requested.
- The sender included an attachment that doesn't make sense.
- The attachment has a dangerous file type.
- The sender asked you to open a link or attachment to avoid a negative consequence or to win a prize.
- The message is unusual and filled with bad grammar and spelling errors.
- The sender asks you to click on a link that seems odd.
- The sender and their message makes you feel uncomfortable.
- The sender asks you to look at a humiliating image of yourself or someone you know.
As you can see, social engineering can trick even the most astute victim. But, now that you’re aware of the red flags, you don’t have to feel vulnerable any longer.
Are you meeting your business goals? Do you have the right processes and systems in place? Is your business growing or is it stagnant? Is your network secure? Whatever goal you are looking to achieve please don’t hesitate to reach out. Please make use of the training materials above and get in contact with us so that we can review your IT Network. You can call us at 201-402-1900 or email us at info@krsit.com.

